Information security organizational structure best practices involve designing a framework that effectively safeguards an organization’s sensitive data and systems from cyber threats. This encompasses establishing clear roles and responsibilities, implementing robust policies and procedures, fostering a culture of security awareness, and ensuring alignment with regulatory requirements and industry standards.
A well-defined structure ensures accountability, promotes collaboration across departments, and enables timely responses to security incidents.
Table of Contents
ToggleThe Importance of Executive-Level Decisions in Information Security

At the executive level, decisions play a crucial role in framing information security organizational structure best practices. By setting strategic priorities and aligning them with security initiatives, leaders ensure that the organization’s security measures contribute directly to its overall goals. This alignment is vital for fostering an environment where security is integrated into daily business processes.
- Risk Management: Prioritize and continuously assess potential security threats.
- Compliance: Ensure all practices are up-to-date with legal and regulatory standards.
- Incident Response: Develop and maintain a robust plan to handle security breaches.
Aligning Security Measures with Business Objectives
Aligning security measures with business objectives is a fundamental aspect of information security organizational structure best practices. By integrating security considerations into the overarching goals of the organization, such as revenue growth, customer satisfaction, and operational efficiency, businesses can ensure that security initiatives are not seen as obstacles but rather as enablers of success.
This alignment facilitates resource allocation, decision-making processes, and risk management strategies that prioritize both security and business needs, ultimately enhancing the organization’s resilience against cyber threats.
Setting Policies and Standards for Information Security
Setting policies and standards for information security is a cornerstone of information security organizational structure best practices. These policies define the rules, guidelines, and procedures that govern the protection of sensitive data and systems within an organization.
By establishing clear expectations and requirements for security practices, organizations can mitigate risks, ensure compliance with regulations, and promote consistency across departments. Furthermore, regularly reviewing and updating these policies in response to evolving threats and technological advancements is crucial to maintaining an effective security posture.
Building an Effective Information Security Team

Building an effective team is central to implementing information security organizational structure best practices. Our team is structured to cover all critical aspects of information security, from incident response to ongoing compliance monitoring, ensuring comprehensive coverage across all our operations. By clearly defining roles and fostering inter-departmental collaboration, we enhance our ability to safeguard organizational assets effectively.
| Role | Responsibilities | Required Skills |
| Security Analyst | Monitor security systems, analyze potential threats | Analytical skills, knowledge of security protocols |
| Incident Responder | Manage responses to security breaches | Problem-solving, decision-making |
| Compliance Officer | Ensure all operations comply with legal standards | Attention to detail, understanding of laws and regulations |
1. Security Roles and Responsibilities
In building an effective information security team, defining clear security roles and responsibilities is paramount within information security organizational structure best practices. This involves assigning specific duties to individuals or teams, such as security analysts, incident responders, compliance officers, and security architects, based on their expertise and organizational needs.
By delineating these roles, organizations can ensure accountability, streamline decision-making processes, and facilitate effective communication and collaboration among team members. Additionally, fostering a culture of shared responsibility for security across the organization further strengthens the effectiveness of the information security team.
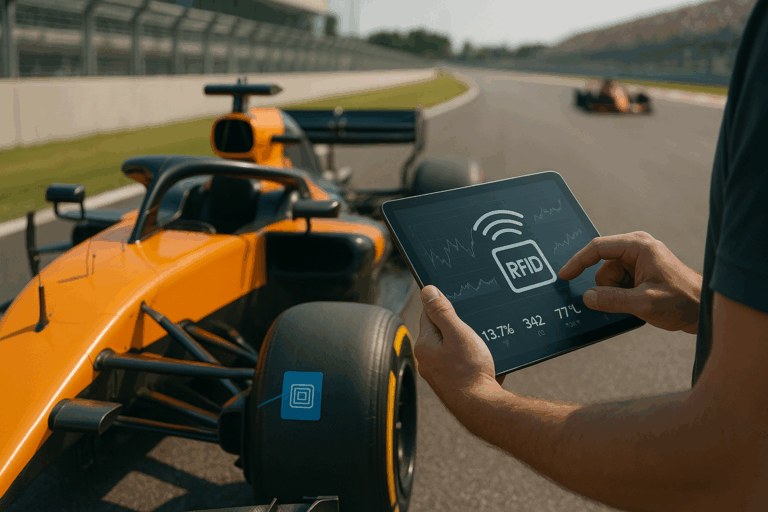
2. Security Resources and Tools
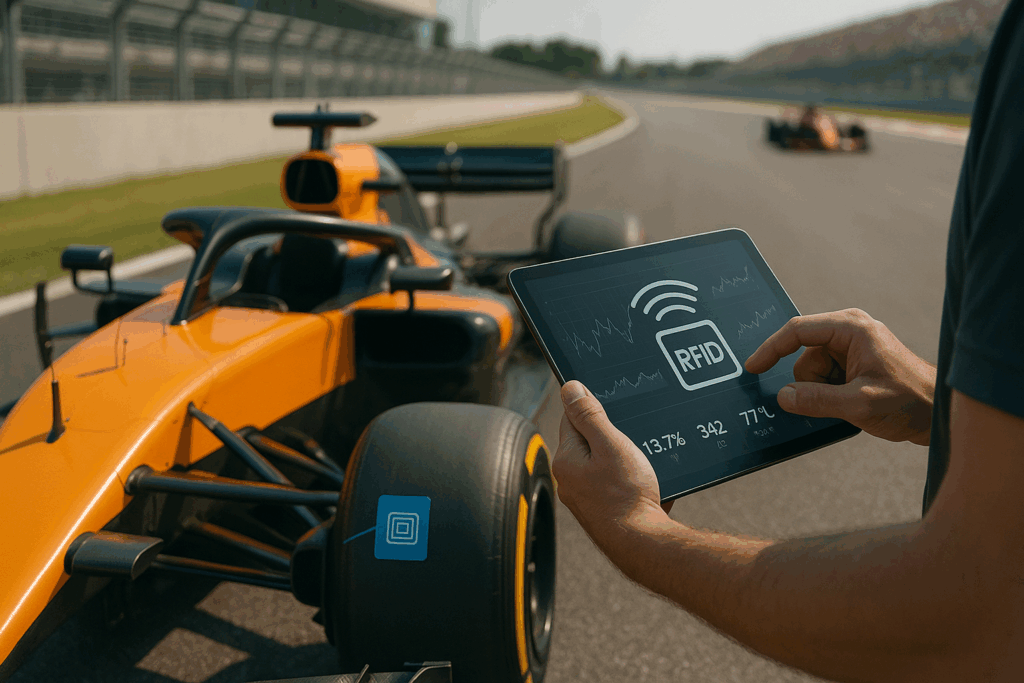
In the context of information security organizational structure best practices, allocating appropriate security resources and utilizing relevant tools are essential components for building a robust defense against cyber threats.
These resources encompass financial investments in technologies, such as firewalls, intrusion detection systems, and encryption tools, as well as human resources, including skilled security professionals and training programs. By aligning resource allocation with identified risks and security priorities, organizations can optimize their security posture and enhance their ability to detect, prevent, and respond to security incidents effectively.
Furthermore, regularly evaluating and updating the arsenal of security tools ensures that the organization remains agile and adaptive in the face of evolving threats and technological advancements.
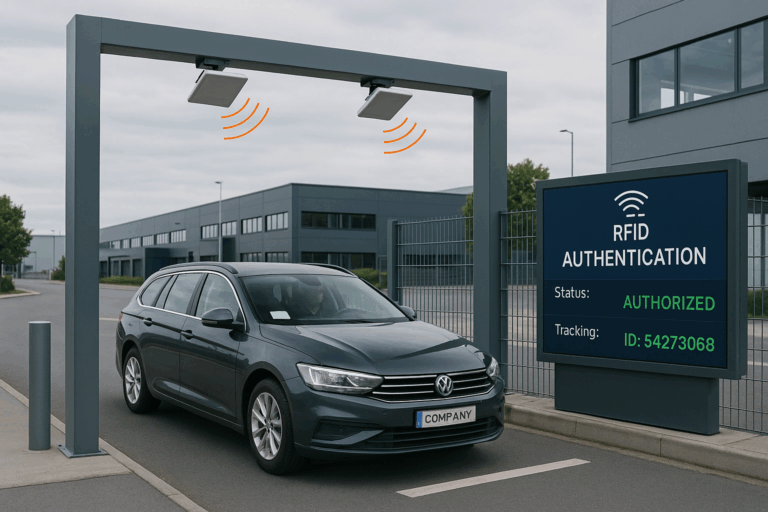
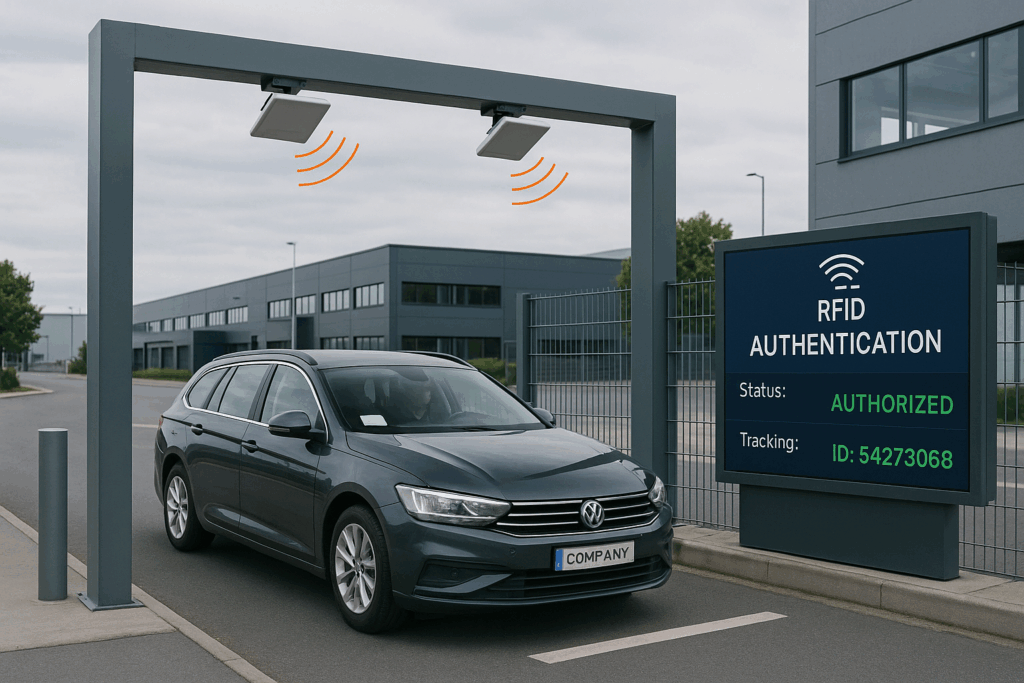
3. Vendor and Contractor Management
Vendor and contractor management plays a critical role in information security organizational structure best practices. This involves establishing clear guidelines and requirements for vendors and contractors who have access to the organization’s systems or handle sensitive data. Implementing thorough vetting processes, including security assessments and due diligence checks, helps ensure that third-party partners adhere to the same security standards as internal staff.
Additionally, incorporating contractual clauses that outline security expectations, data protection measures, and incident response procedures is essential for holding vendors and contractors accountable for maintaining the confidentiality, integrity, and availability of the organization’s information assets. Regular monitoring and oversight of vendor activities further mitigate risks associated with third-party relationships and enhance overall security resilience.
Risk Management in Information Security Organizational Structure

Risk management is a cornerstone of our information security organizational structure best practices. We focus on identifying, assessing, and mitigating risks systematically to protect our assets and data. This proactive approach allows us to stay ahead of potential threats and ensure the security and continuity of our operations.
Phishing Attacks: Implement regular training sessions and simulation exercises.
Data Breaches: Use encryption and strong access controls.
Ransomware: Maintain up-to-date backups and employ anti-malware tools.
1. Risk Register and Assessment
In the realm of information security organizational structure best practices, maintaining a comprehensive risk register, and conducting regular risk assessments are vital components. A risk register serves as a centralized repository for documenting identified risks, their potential impact, and mitigation strategies. By systematically assessing threats and vulnerabilities, organizations can prioritize security initiatives and allocate resources effectively.
Furthermore, conducting regular risk assessments enables organizations to stay ahead of emerging threats, adapt to changing business environments, and ensure compliance with regulatory requirements. Integrating risk management into the organization’s decision-making processes fosters a proactive approach to addressing security challenges and enhances overall resilience against cyber threats.
2. Vulnerability Scanning and Penetration Testing
Vulnerability scanning and penetration testing are crucial elements of information security organizational structure best practices. Vulnerability scanning involves systematically scanning networks, systems, and applications to identify known vulnerabilities that could be exploited by attackers.
Penetration testing, on the other hand, involves simulating real-world cyber attacks to identify potential security weaknesses and assess the effectiveness of existing security controls.
By conducting regular vulnerability scans and penetration tests, organizations can proactively identify and remediate security vulnerabilities before they are exploited by malicious actors. This proactive approach helps strengthen the organization’s security posture, reduce the likelihood of successful cyber attacks, and protect sensitive data and systems from unauthorized access or compromise.
Information Security Governance and Compliance

Governance and compliance are critical elements of our information security organizational structure best practices. We adhere to international standards and regulatory requirements to manage risks and protect sensitive information. Our governance framework ensures that security policies are consistently applied across all levels of the organization.
| Framework/Standard | Description | Main Requirements |
| ISO 27001 | International standard for information security | Risk assessment, security controls, management commitment |
| GDPR | General Data Protection Regulation in EU | Data protection, rights of individuals, data breach notifications |
| HIPAA | Health Insurance Portability and Accountability Act | Secure handling of health information, privacy safeguards |
Compliance Standards and Regulations
Information security governance and compliance are integral aspects of information security organizational structure best practices.
Governance frameworks provide the structure, processes, and oversight mechanisms necessary to ensure that information security aligns with organizational objectives and meets regulatory requirements. Compliance with relevant standards and regulations, such as ISO 27001, GDPR, HIPAA, and PCI DSS, is essential for safeguarding sensitive data and maintaining trust with customers, partners, and regulatory bodies.
By implementing robust compliance programs, organizations demonstrate their commitment to protecting information assets, mitigating risks, and adhering to legal and industry-specific obligations. Regular audits and assessments help verify compliance status and identify areas for improvement, enabling organizations to continuously enhance their security posture and mitigate compliance-related risks.
Program Maturity and Metrics
Program maturity and metrics are essential components of information security organizational structure best practices. Assessing the maturity of security programs allows organizations to evaluate their effectiveness and identify areas for improvement. This involves evaluating various aspects, such as policies and procedures, security awareness training, incident response capabilities, and technology infrastructure.
Additionally, establishing meaningful security metrics enables organizations to measure and track progress toward security goals, identify trends, and make informed decisions to enhance security posture.
By regularly reviewing program maturity and metrics, organizations can adapt to evolving threats, demonstrate the value of security investments, and effectively communicate with stakeholders about the organization’s security posture and performance.
Security Architecture and Controls

Our security architecture and controls are designed according to information security organizational structure best practices. We implement robust measures such as data loss prevention and intrusion detection to safeguard our networks and data against cyber threats, ensuring the integrity and availability of our information assets.
- Firewalls: Block unauthorized access to network resources.
- Encryption: Protect data integrity and confidentiality during storage and transmission.
- Access Controls: Restrict and monitor who can view and use company resources.
Data Loss Prevention Techniques
Security architecture and controls are foundational elements of information security organizational structure best practices. Within this framework, implementing data loss prevention (DLP) techniques is crucial for protecting sensitive information from unauthorized disclosure, modification, or exfiltration.
DLP solutions encompass a range of technologies and strategies designed to monitor, detect, and prevent the unauthorized transmission or storage of sensitive data. These techniques may include encryption, access controls, data classification, monitoring, and logging, as well as user activity monitoring.
By deploying DLP measures effectively, organizations can mitigate the risk of data breaches, regulatory non-compliance, and reputational damage, while also safeguarding the confidentiality, integrity, and availability of their critical information assets.
Intrusion Detection and Prevention Systems
Intrusion detection and prevention systems (IDPS) are essential components of information security organizational structure best practices.
These systems continuously monitor network traffic and system activity to detect and respond to potential security threats in real time. Intrusion detection systems (IDS) analyze network traffic patterns and behavior to identify suspicious activities indicative of unauthorized access, malware infections, or other cyber threats. Meanwhile, intrusion prevention systems (IPS) not only detect but also automatically block or mitigate identified threats to prevent them from compromising the organization’s systems or data.
By deploying IDPS effectively, organizations can enhance their ability to detect and thwart cyber attacks, minimize the impact of security incidents, and maintain the integrity and availability of their IT infrastructure.
Security Awareness, Training, and Culture
Cultivating a strong security culture through ongoing awareness and training is essential to our information security organizational structure best practices. We empower our employees with the knowledge and tools they need to recognize and react to security threats, making them a proactive defense against potential breaches.
1. Employee Training Programs
Security awareness, training, and culture are critical aspects of information security organizational structure best practices. Within this framework, employee training programs play a pivotal role in educating staff about cybersecurity risks, best practices, and their roles and responsibilities in safeguarding organizational assets.
These programs may include interactive workshops, online courses, simulated phishing exercises, and other educational initiatives tailored to different roles and levels of expertise within the organization.
By fostering a culture of security awareness and continuous learning, organizations can empower employees to recognize and respond to security threats effectively, thereby reducing the likelihood of human error leading to security incidents.
Additionally, regular training helps reinforce security policies and procedures, promotes adherence to compliance requirements, and strengthens the overall security posture of the organization.
2. Creating an Information Security Culture
Creating an information security culture is paramount within information security organizational structure best practices. This involves fostering a mindset where security is viewed as everyone’s responsibility, from top-level executives to frontline employees.
Key elements of cultivating such a culture include promoting awareness of security risks and best practices, providing ongoing training and education, and encouraging open communication about security concerns.
By integrating security into the organization’s values, norms, and daily operations, employees become more vigilant and proactive in identifying and mitigating security threats.
Moreover, recognizing and rewarding behaviors that prioritize security reinforces the importance of maintaining a strong security posture throughout the organization. Ultimately, a robust information security culture enhances resilience against cyber threats and strengthens the overall security posture of the organization.
- Interactive Workshops: Engage employees in learning about cybersecurity risks and prevention.
- Simulated Phishing Exercises: Train employees to identify and respond to phishing attempts.
- Role-Specific Training: Tailor security training according to the specific roles and responsibilities of employees.
Incident Response and Business Continuity
Our incident response and business continuity plans are integral to our information security organizational structure best practices. We prepare for potential disruptions with detailed response strategies and robust recovery solutions to minimize impact and maintain critical operations under all circumstances.
Incident Response Plans
Incident response plans are vital components of information security organizational structure best practices, especially in conjunction with business continuity strategies.
These plans outline the steps to be taken in the event of a security incident, such as a data breach, malware outbreak, or system compromise, to minimize the impact on operations and mitigate further damage. Key elements of incident response plans include roles and responsibilities of personnel, escalation procedures, communication protocols, containment and eradication measures, and post-incident analysis and recovery strategies.
By proactively developing and regularly testing incident response plans, organizations can streamline response efforts, reduce downtime, and mitigate financial and reputational losses associated with security incidents. Additionally, integrating incident response with broader business continuity efforts ensures a holistic approach to resilience, enabling the organization to maintain essential functions and services during and after a disruptive event.
| Element | Incident Response | Business Continuity |
| Purpose | Manage immediate security incidents | Ensure continuation of operations |
| Key Actions | Identification, containment, eradication | Disaster recovery, maintaining critical functions |
| Expected Outcomes | Minimize impact, learn from events | Quick recovery and minimal disruption |
Business Continuity and Disaster Recovery
Business continuity and disaster recovery planning are essential components of information security organizational structure best practices. These plans ensure that organizations can continue essential operations and services in the face of disruptions caused by natural disasters, cyber-attacks, or other emergencies.
Business continuity plans outline strategies and procedures for maintaining critical functions, while disaster recovery plans focus on restoring IT infrastructure and systems following a disruptive event. Key elements of these plans include risk assessments, backup and recovery procedures, alternative workspace arrangements, communication protocols, and testing and exercising to ensure effectiveness.
By investing in robust business continuity and disaster recovery measures, organizations can minimize downtime, mitigate financial losses, and preserve their reputation in the event of a crisis. Additionally, integrating these plans with incident response efforts ensures a coordinated and comprehensive approach to resilience and recovery.
Get in Touch for a Free Quote
At CPCON, we’ve established a robust information security organizational structure grounded in decades of expertise in fixed asset management and stock control. We set clear roles and responsibilities, align our security measures with our strategic business objectives, and enforce comprehensive policies and standards to uphold information security governance and compliance.
We prioritize allocating the right security resources and utilizing the best tools available. Managing our vendors and contractors effectively is crucial to mitigate risks associated with third-party interactions. By implementing thorough risk management practices, including regular assessments and maintaining a risk register, we ensure that our security initiatives are prioritized and compliant with regulations.
Building a strong security culture through ongoing employee training programs and promoting awareness of security risks and best practices are central to our strategy. Additionally, our integrated approach to incident response and business continuity planning enables us to maintain resilience and ensure a coordinated recovery in the event of security incidents or disasters.
By adhering to these best practices, we not only enhance our security posture but also protect our sensitive data and systems, effectively mitigating cyber threats. To learn more about how we can help secure your assets, contact us today.
Frequently Asked Questions (FAQs)
How do I align my information security measures with my business objectives?
To align information security measures with business objectives, conduct a thorough assessment of organizational goals and risks, then prioritize security initiatives that support those objectives while mitigating identified risks.
What are the key roles and responsibilities of an information security team?
Key roles and responsibilities in an information security team typically include security analysts, incident responders, compliance officers, and security architects, each tasked with specific duties to protect the organization’s assets and systems.
How do I conduct a risk assessment for my information security structure?
To conduct a risk assessment for your information security structure, identify potential threats and vulnerabilities, assess their likelihood and impact, prioritize them based on severity, and develop mitigation strategies accordingly.
What compliance standards should my organization adhere to?
Your organization should adhere to relevant compliance standards such as ISO 27001, GDPR, HIPAA, and PCI DSS, based on the industry and geographic location, to ensure legal and regulatory compliance and safeguard sensitive data.
How do I create a culture of information security awareness within my organization?
To create a culture of information security awareness, provide regular training and education to employees, promote open communication about security risks, and incentivize adherence to security policies and procedures through recognition and rewards.